How to login to stacker.news programmatically
Using Python, LNbits, curlconverter, and Burp Suite.
stacker.news is an online forum where users share stories, resources, and news about Bitcoin or topics related to Bitcoin. However, instead of upvoting or liking posts, users tip each others’ posts with Bitcoin. Users also pay to submit posts, which acts as a mechanism for limiting spam. The first few interactions with the website are free. Afterwards, users can deposit Bitcoin or earn it from others by providing valuable content during the ‘free trial’. All contributions are voluntary. Furthermore, active users receive an airdrop every day.
This article describes how to ‘log in’ to stacker.news using only Python requests. It uses LNbits, a FOSS lightning wallet, Burp Suite, a penetration testing software, and curlconverter, an online tool to convert curl commands to any programming language.
Create an LNbits wallet
LNbits is a free and open source lightning wallet. Their website itself hosts a demo server where anyone can create a wallet, add extensions, and explore using lightning. We’ll be using the Legend demo server to create a wallet. This wallet will be used to login to stacker.news via LNURL.
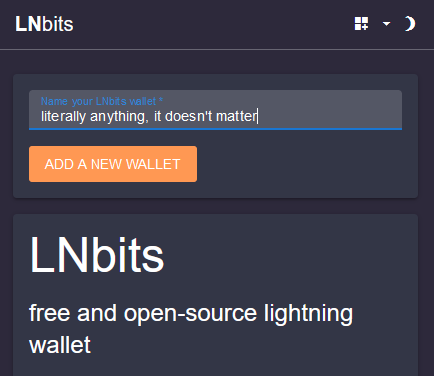
From the Legend demo site, give the wallet a name.
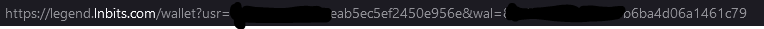
Bookmark the next page!! This URL lets you access your wallet when you close the browser. It should look something like this:
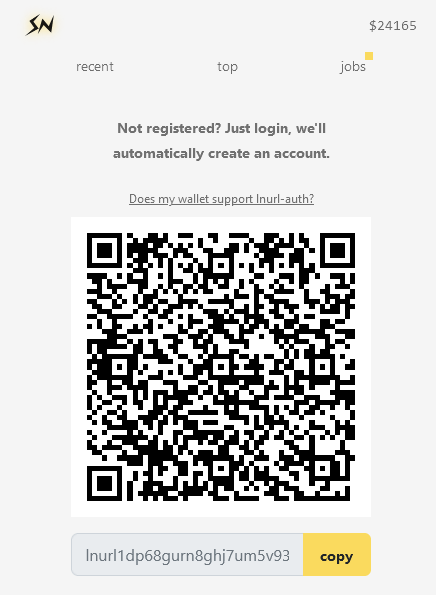
Logging in manually via LNURL
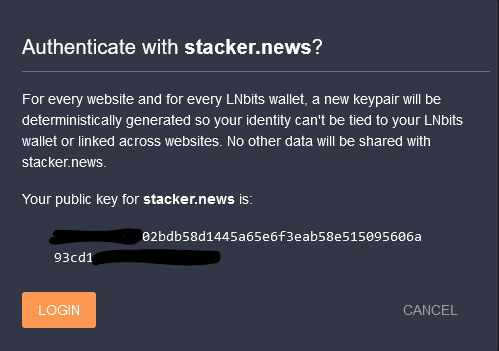
LNURL-auth is a login method where the user proves their identity by signing a randomly generated message from the website using the private key of their wallet (in this case LNbits).
Copy the LNURL, paste it as an invoice in LNbits, and it will ask if you want to authenticate with stacker.news. Click Login and stacker.news will refresh and you will be logged in to your (perhaps newly generated) account.
Using Burp Suite to see what’s happening in the background
Burp Suite is a graphical tool for performing security testing of web applications. It’s a really useful tool for web scraping and creating unofficial API wrappers.
Usually it’s enough to use the Networking tab in Firefox debugger, but Burp has some features to make reverse engineering easier, including a sitemap generator, HTTP history, and intercept mode.
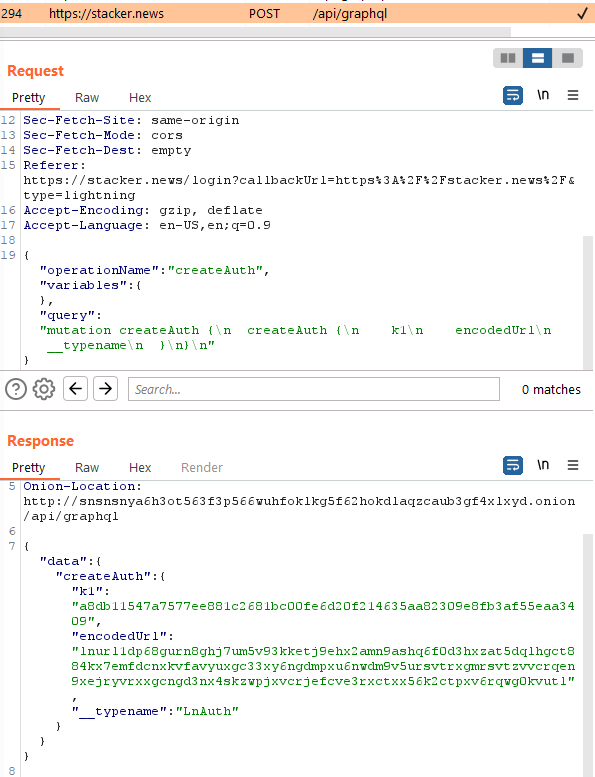
When logging into stacker.news, the website sends a request to its GraphQL database to create a new LNURL-auth, which is returned in the response in JSON. “k1” is the random message, “encodedURL” contains the callback URL to submit the signed message.
Replaying this request as a curl command will generate new LNURLs. This curl command can be converted to Python using curlconverter.
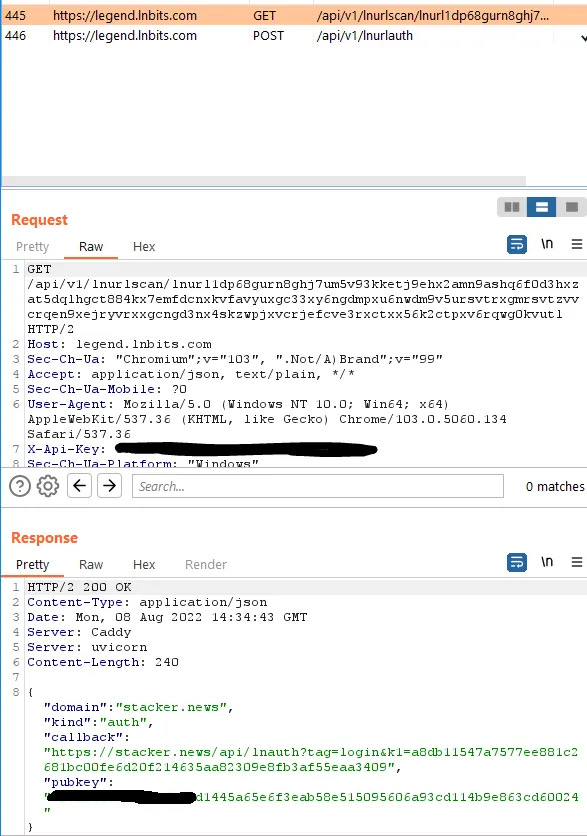
When the LNURL is submitted as an invoice to LNbits it goes through two stages: decoding, and authorization. The decoding stage gets the random message and callback URL from the LNURL. The authorization stage signs the message and submits it to the callback URL, in this case, stacker.news.
Once again, these requests can be copied as curl commands and converted to Python to submit arbitrary LNURLs for authentication.
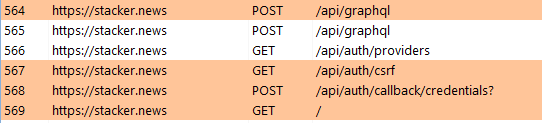
stacker.news repeatedly queries the GraphQL database to see if the message has been signed and if so, by whom. When it detects a signed message, it generates a csrf token, associates it with pubkey of the signee, and submits this information in exchange for a secure authorization cookie that can then be used to submit posts, comments, and, in general, update the GraphQL database within the user’s permissions.
These requests can also be copied as curl commands, converted, and replayed to create logged in sessions via Python.
The conversion and linking of these commands is left as an exercise for the reader. (:
All in all, this project took about 3 hours to complete. At $50/hour, this project is worth… something. With this script, you could create accounts ad infinitum, each with 2 free posts and 5 free comments. If accounts are free, and posts are free, is the spam problem truly solved?
If you found this article interesting, consider tipping me on stacker.news! As always, technical corrections or questions are welcome.